
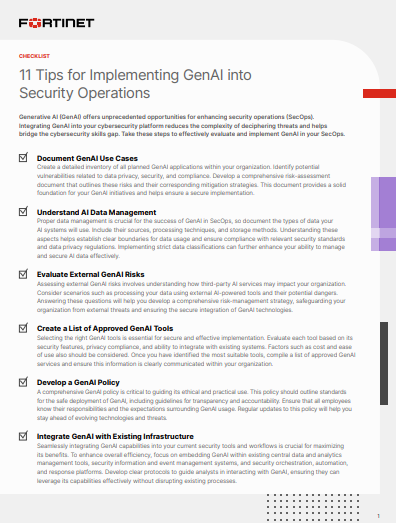
11 Tips for Implementing GenAI into Security Operations
Maximize your security investments
Seamlessly integrate advanced AI capabilities into your existing infrastructure by:
Seamlessly integrate advanced AI capabilities into your existing infrastructure by:
- Documenting use cases
- Identifying approved tools
- Developing policies
- Automating routine tasks
- Enhancing investigation
- Improving response
Thank You For Your Interest
You have been directed to this site by DemandBytes. For more details on our information practices, please see our Privacy Policy, and by accessing this content you agree to our Terms of Use. You can unsubscribe at any time.

